14.3 Configuring SSL Communication with the Browsers and the Identity Server
-
In the Administration Console, click > > > .
-
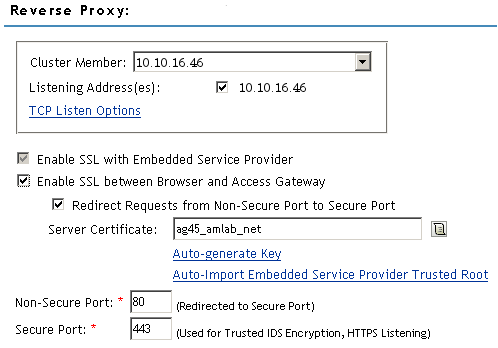
Configure the reverse proxy for SSL. Fill in the following fields:
Enable SSL with Embedded Service Provider: Select this option to encrypt the data exchanged for authentication (the communication channel between the Identity Server and the Access Gateway). This option is only available for the reverse proxy that has been assigned to perform authentication.
If you enable SSL between the browsers and the Access Gateway, this option is automatically selected for you. You can enable SSL with the embedded service provider without enabling SSL between the Access Gateway and the browsers. This allows the authentication and identity information that the Access Gateway and the Identity Server exchange to use a secure channel, but allows the data that the Access Gateways retrieves from the back-end Web servers and sends to users to use a non-secure channel. This saves processing overhead if the data on the Web servers is not sensitive.
Enable SSL between Browser and Access Gateway: Select to require SSL connections between your clients and the Access Gateway. SSL must be configured between the browsers and the Access Gateway before you can configure SSL between the Access Gateway and the Web servers.
Redirect Requests from Non-Secure Port to Secure Port: Determines whether browsers are redirected to the Secure Port and allowed to establish an SSL connection. If this option is not selected, browsers that connect to the non-secure port are denied service.
This option is only available if you have selected .
-
Select the certificate to use for SSL between the Access Gateway and the browsers. Select one of the following methods:
-
To auto-generate a certificate key by using the Access Manager CA, click , then click twice. The generated certificate appears in the text box.
The generated certificate uses the published DNS name of the first proxy service for the Subject name of the certificate. If there is more than one proxy service, the CA generates a wildcard certificate (*.Cookie Domain).
If you have not created a proxy service for this reverse proxy, wait until you have created a proxy service before generating the key. This allows the CN in the field of the certificate to match the published DNS name of the proxy service.
-
To select a certificate, click the icon, select the certificate you have created for the DNS name of your proxy service, then click . The certificate appears in the text box. For SSL to work, the CN in the Subject field of the certificate must match the published DNS name of the proxy service.
-
-
(Conditional) If you have selected a certificate in Step 3 that was created by an external CA, click , click , specify an alias name, click , then click .
This option imports the public key from the embedded service provider into the trust store of the Identity Servers in the selected Identity Server Configuration. This sets up a trusted SSL relationship between the Identity Server and the embedded service provider.
If you are using certificates signed by the Novell Access Manager CA, the public key is automatically added to this trust store.
-
Configure the ports for SSL:
Non-Secure Port: Specifies the port on which to listen for HTTP requests. The default port for HTTP is 80.
-
If you have selected the option, requests sent to this port are redirected to the secure port. If the browser can establish an SSL connection, the session continues on the secure port. If the browser cannot establish an SSL connection, the session is terminated.
-
If you do not select the option, this port is not used when SSL is enabled.
IMPORTANT:If you select not to redirect HTTP requests (port 80) and your Access Gateway has only one IP address, do not use port 80 to configure another reverse proxy. Although it is not used, it is reserved for this reverse proxy.
Secure Port: Specifies the port on which to listen for HTTPS requests (usually 443). This port needs to match the configuration for SSL. If SSL is enabled, this port is used for all communication with the browsers. The listening address and port combination must not match any combination you have configured for another reverse proxy or tunnel.
-
-
Click .
-
On the page, click .
-
(Conditional) If you are using an externally signed certificate for the Identity Server cluster, you need to import the public key of the CA;
-
In the section, click , then click
-
Specify an alias, click twice, then click .
This option imports the public key of the Identity Server into the trust store of the embedded service provider. This sets up a trusted SSL relationship between the embedded service provider and the Identity Server.
The configCA public key certificate of the Access Manager CA is automatically added to the ESP Trust Store. If you are using Access Manager CA certificates for the Identity Server, you do not need to import the configCA certificate unless someone has deleted it from this trust store.
-
-
Click .
-
On the Server Configuration page, click .
-
On the Access Gateways page, click > .
The embedded service provider is restarted during the update.
-
Update the Identity Server so that it uses the new SSL configuration. Click > .
-
Verify that the trusted relationship between the Identity Server and the Access Gateway has been reestablished.
-
Enter the URL to a protected resource on the Access Gateway.
-
Complete one of the following:
-
If you are prompted for login credentials, enter them. The trusted relationship has been reestablished.
-
If you receive a 100101043 or 100101044 error, the trusted relationship has not been established. For information on solving this problem, see
Troubleshooting 100101043 and 100101044 Liberty Metadata Load Errors
in the Novell Access Manager 3.0 SP4 Administration Guide.
-
-
-
To configure additional security options, continue with one of the following: