17.1 Controlling Access to Services
OES 2 supports a number of options for service access, including
-
Web browsers.
-
File managers and applications on Linux, Macintosh, and Windows workstations.
-
Novell Client software.
-
Personal digital assistants (PDAs) and other electronic devices that are enabled for Web access.
You control which of these options can be used through the services you offer and the ways your configure those services.
This section can help you understand access control at a high level so that you can plan, implement, and control access to services. More detail about the items discussed is contained in individual service guides.
The topics that follow are:
17.1.1 Overview of Access Control
The following sections present overviews of methods for accessing Open Enterprise Server 2 services.
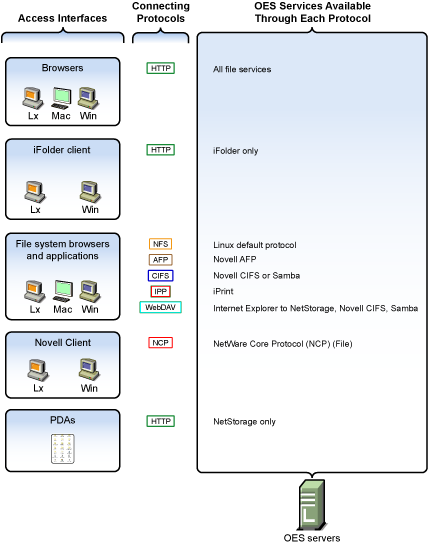
Access to OES 2 Services
Figure 17-1 illustrates the access methods supported by OES 2 services. Novell eDirectory provides authentication to each service.
Figure 17-1 Access Interfaces and the Services They Can Access

The interfaces available for each service are largely determined by the protocols supported by the service.
-
Browsers and personal digital assistants require support for the HTTP protocol.
-
Each workstation type has file access protocols associated with it. Linux uses NFS as its native protocol for file services access, Macintosh workstations communicate using AFP or CIFS, and Windows workstations use the CIFS protocol for file services.
-
Novell Client software for both Windows and Linux uses the NetWare Core Protocol (NCP) to provide the file services for which Novell is well known.
Understanding the protocol support for OES 2 services can help you begin to plan your OES implementation. For more information, see Matching Protocols and Services to Check Access Requirements.
Access Control Options in OES 2
Because OES 2 offers both traditional Novell access control and POSIX access control, you have a variety of approaches available to you, including combining the two models to serve various aspects of your network services.
Table 17-1 provides links to documentation that discusses OES 2 access control features.
Table 17-1 General File System Access Control
|
Feature |
To Understand |
See |
|---|---|---|
|
Access Control Lists (ACLs) on Linux |
How ACLs are supported on the most commonly used Linux POSIX file systems and let you assign file and directory permissions to users and groups who do not own the files or directories. |
|
|
Aligning NCP and POSIX access rights |
How to approximate the NCP (or NetWare) access control model on POSIX file systems. |
|
|
Directory and file attributes |
Directory and file attributes on NSS volumes. |
|
|
File system trustee rights |
File system trustee rights on NetWare (NSS and traditional volumes), including how effective file system trustee rights are determined. |
|
|
Novell trustee rights and directory and file attributes |
How to control who can see which files and what they can do with them. |
|
|
POSIX file system rights and attributes on Linux |
How to configure file system attributes on OES 2 servers. |
|
|
Security Equivalence in eDirectory |
The concept of Security Equivalence in eDirectory. |
|
The Traditional Novell Access Control Model
NetWare is known for its rich access control. OES makes these controls available on Linux through NSS volume support. In addition, some of the controls are available on Linux POSIX file systems through NCP volume creation. NCP volumes are limited because Linux POSIX systems offer only a subset of the directory and file attributes that NSS offers.
In the Novell access control model, eDirectory objects, such as users and groups, are assigned File System Trustee Rights to directories and files on NSS and NCP volumes. These trustee rights determine what the user or group can do with a directory or file, provided that the directory or file attributes allow the action.
This is illustrated in Figure 17-2.
Figure 17-2 Directory and File Access under the NetWare Access Control Model
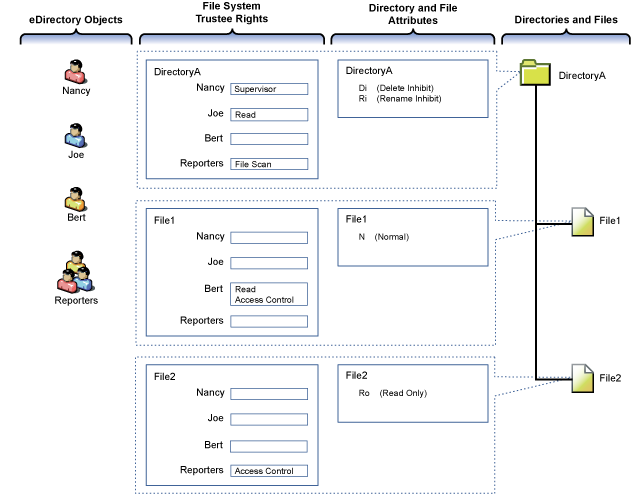
Table 17-2 explains the effective access rights illustrated in Figure 17-2.
Table 17-2 Access Rights Explanation
|
eDirectory Objects |
File System Trustee Rights |
Directory and File Attributes |
Directories and Files |
|---|---|---|---|
|
eDirectory objects (in most cases users and groups) gain access to the file system through eDirectory. |
File system trustee rights govern access and usage by the eDirectory object specified for the directory or file to which the rights are granted. Trustee rights are overridden by directory and file attributes. For example, even though Nancy has the Supervisor (all) trustee right at the directory (and, therefore, to the files it contains), she cannot delete File2 because it has the Read Only attribute set. Of course, Nancy could modify the file attributes so that File2 could then be deleted. |
Each directory and file has attributes associated with it. These attributes apply universally to all trustees regardless of the trustee rights an object might have. For example, a file that has the Read Only attribute is Read Only for all users. Attributes can be set by any trustee that has the Modify trustee right to the directory or file. |
The possible actions by the eDirectory users and group shown in this example are as follows:
|
NSS Access Control on OES
Table 17-3 provides links to documentation that discusses the various NSS-specific access control features.
Table 17-3 Summary of NSS Access Control Documentation Links
|
Feature |
To Understand |
See |
|---|---|---|
|
Independent Mode vs. NetWare Mode This applies only to OES servers, not NetWare. |
The difference between Independent Mode access and NetWare Mode access. |
|
|
POSIX directory and file attributes on NSS volumes on OES 2 This is only about what is displayed. POSIX permissions are not used for access control to NSS volumes. |
How NSS file attributes are reflected in Linux directory and file permissions viewable through POSIX. |
|
Novell Client (NCP File Services) Access
If you have not already determined whether to use the Novell Client on your network, we recommend that you consider the following information:
About the Novell Client
The Novell Client extends the capabilities of Windows and Linux desktops with access to NetWare and OES 2 servers.
After installing Novell Client software, users can enjoy the full range of Novell services, such as
-
Authentication via Novell eDirectory
-
Network browsing and service resolution
-
Secure and reliable file system access
-
Support for industry-standard protocols
The Novell Client supports the traditional Novell protocols (NDAP, NCP, and RSA) and interoperates with open protocols (LDAP, CIFS, and NFS).
Is the Novell Client Right for Your Network?
Although Novell offers services that don’t require Novell Client, (such as NetStorage, Novell iFolder 3.8, and iPrint), many network administrators continue to prefer the Novell Client as the access choice for their network users for the following reasons:
-
They prefer eDirectory authentication to LDAP authentication because they believe it is more secure.
-
They prefer the NetWare Core Protocol (NCP) over the Microsoft CIFS protocol because they believe that CIFS is more vulnerable to the propagation of viruses on the network.
Conversely, other network administrators are equally adamant that their users function better without the added overhead of running an NCP client on each workstation.
We can’t determine what is best for you or your network, but we do provide you with viable choices.
Differences between Linux and Windows
There are some differences between the Linux and Windows clients. These are documented in Understanding How the Novell Client for Linux Differs from the Novell Client for Windows 2000/XP
in the Novell Client 2.0 SP3 for Linux Administration Guide.
eDirectory User Access to OES 2 Servers
Some services that run on OES 2 servers require that the users accessing them be (or, at least, appear to the Linux system to be) standard Linux users with Linux user credentials, such as a user ID (UID) and primary group ID (GID).
So that eDirectory users can access these services, Novell provides the Linux User Management (LUM) technology. The impact of this on you as the network administrator is that these users and groups must be enabled for eDirectory LDAP authentication to the local server. For more information, see Linux User Management: Access to Linux for eDirectory Users.
17.1.2 Planning for Service Access
After you understand the access options available to your network users, you can decide which will work best on your network.
Planning tips for network services are contained in the following sections:
Planning File Service Access
As you plan which file services to provide, be aware of the file service/volume and feature support limitations outlined in the following sections.
Service Access to Volume Type Limitations
Supported combinations are outlined in Table 17-4.
Table 17-4 Service Access to Volume Types
|
File Service |
Linux POSIX Volumes |
NSS Volumes on Linux |
|---|---|---|
|
AFP |
No |
Yes-Novell AFP |
|
CIFS |
Yes-Novell CIFS, Novell Samba |
Yes-Novell CIFS, Novell Samba |
|
NetStorage |
Yes |
Yes |
|
NetWare Core Protocol (NCP) |
Yes |
Yes |
|
NFS |
Yes |
Yes-NFSv3 |
|
Novell iFolder 2.1x |
No |
No |
|
Novell iFolder 3.8 |
Yes |
Yes |
Details about the file systems supported by each file service are explained in the documentation for each service.
Be aware that file services support different sets of access protocols. A summary of the protocols available for access to the various OES file services is presented in Matching Protocols and Services to Check Access Requirements.
Feature Support
Table 17-5 Features Supported on Each Volume Type
|
Feature |
Linux POSIX Volumes |
NSS Volumes on Linux |
|---|---|---|
|
Directory quotas |
No |
Yes |
|
Login scripts |
Yes (if also defined as an NCP volume) |
Yes |
|
Mapped drives |
Yes (if also defined as an NCP volume) |
Yes |
|
Novell directory and file attributes |
No |
Yes |
|
Purge/Salvage |
No |
Yes |
|
Trustee rights |
Yes (if also defined as an NCP volume) |
Yes |
|
User space quotas |
No |
Yes |
Planning Print Service Access
Novell iPrint has access control features that let you specify the access that each eDirectory User, Group, or container object has to your printing resources.
You can also use iPrint to set up print services that don’t require authentication.
NOTE:Access control for printers is supported only on the Windows iPrint Client.
For more information on access control and iPrint, see Setting Access Control for Your Print System
in the OES 2 SP3: iPrint for Linux Administration Guide
Matching Protocols and Services to Check Access Requirements
Figure 17-3 illustrates the access interfaces available to users in OES and the services that each interface can connect to. It also shows the protocols that connect access interfaces with network services.
To use this for planning:
-
Review the different access interfaces in the left column.
-
In the middle column, review the protocols each interface supports.
-
In the right column, view the services available to the interfaces via the protocols.
Figure 17-3 Access Interfaces and Services, and the Protocols That Connect Them
17.1.3 Coexistence and Migration of Access Services
Because NetWare Core Protocol (NCP) is now available on Linux, your Novell Client users can attach to OES 2 servers as easily as they have been able to attach to NetWare servers. In fact, they probably won’t notice any changes.
NCP Server for Linux enables support for login scripts, mapping drives to OES 2 servers, and other services commonly associated with Novell Client access. This means that Windows users with the Novell Client installed can now be seamlessly transitioned to file services on OES 2. And with the Novell Client for Linux, Windows users can be moved to SUSE Linux Enterprise Desktop with no disruption in NCP file services.
For more information, see the OES 2 SP3: NCP Server for Linux Administration Guide.
17.1.4 Access Implementation Suggestions
After you plan and install OES 2 services, be sure to provide clear access instructions to your network users. For a summary of access methods, see Section E.0, Quick Reference to OES 2 User Services.
17.1.5 Configuring and Administering Access to Services
The following sections discuss administering access to services.
Password Management
Many network administrators let users administer their own passwords. For more information on password self management, see Password Self-Service
in the Novell Password Management 3.3.2 Administration Guide.
Linux (POSIX) File System Access Rights
Access control to Linux POSIX file systems is controlled through POSIX file system access rights or attributes associated with directories and files. In general, the directories and files can be accessed by three POSIX entities:
-
The user who owns the directory or file
-
The group who owns the directory or file
-
All other users defined on the system
These users and the affected group are each assigned (or not assigned) a combination of three attributes for each directory and file:
Table 17-6 Linux Access Rights
|
Attribute |
Effect on Directory when Assigned |
Effect on File when Assigned |
|---|---|---|
|
Read |
Lets the user or group view the directory's contents. |
Lets the user or group open and read the file. |
|
Write |
Lets the user or group create or delete files and subdirectories in the directory. |
Lets the user or group modify the file. |
|
Execute |
Lets the user or group access the directory by using the cd command. |
Lets the user or group run the file as a program. |
For more information, see Configuring Trustees and File System Attributes
in the OES 2 SP3: File Systems Management Guide.
NSS File and Directory Trustee Management
The OES 2 SP3: File Systems Management Guide contains a thorough discussion of file and directory trustee management in its Configuring Trustees and File System Attributes
section.
The following sections present brief information about managing trustees on NSS volumes.
Using NetStorage to Change File and Directory Attributes and Trustees
You can use the NetStorage Web browser interface to change attributes and trustees for directories and files on NSS volumes, but you can’t change them by using a WebDAV connection to NetStorage.
Using the Novell Client to Change File and Directory Attributes and Trustee Rights
You can use the Novell Client to change NSS file and directory attributes and to grant trustee rights to an NSS volume on an OES 2 server. For more information, see NetWare File Security
in the Novell Client 4.91 SP5 for Windows XP/2003 Installation and Administration Guide and Managing File Security
in the Novell Client 2.0 SP3 for Linux Administration Guide.
Using iManager 2.7 to Change File and Directory Attributes and Trustee Rights
You can use the iManager 2.7 Files and Folders plug-in to manage directories and files on NCP and NSS volumes. For more information, see the plug-in help.
Using the Linux Command Prompt to Change File Attributes
Use the attrib command to change file and directory attributes on an NSS volume.
The attrib command is also documented in Using the Attrib Utility to Set NSS File System Attributes
in the OES 2 SP3: File Systems Management Guide.
You can also enter the following command at the command prompt:
attrib --help
Using the Linux Command Prompt to Change Trustee Rights
To grant NSS trustee rights to an NSS volume, enter the following command:
rights -f /full/directory/path -r rights_mask trustee full.object.context
where /full/directory/path is the path to the target directory on the NSS volume, rights_mask is the list of NSS rights, and full.object.context is the object (User or Group) in its full eDirectory context including the tree name.
For example, you might enter the following:
rights -f /data/groupstuff -r rwfc trustee mygroup.testing.example_tree
For a complete list of command options, enter rights at the command prompt.
The rights command is also documented in Using the Rights Utility to Set Trustee Rights for the NSS File System
in the OES 2 SP3: File Systems Management Guide.