14.1 Understanding the File Inventory for a Shadow Volume
The inventory provides key statistics about the files in the selected volume, such as files scanned and the available space trends. The inventory includes the following information:
14.1.1 Inventory Summary
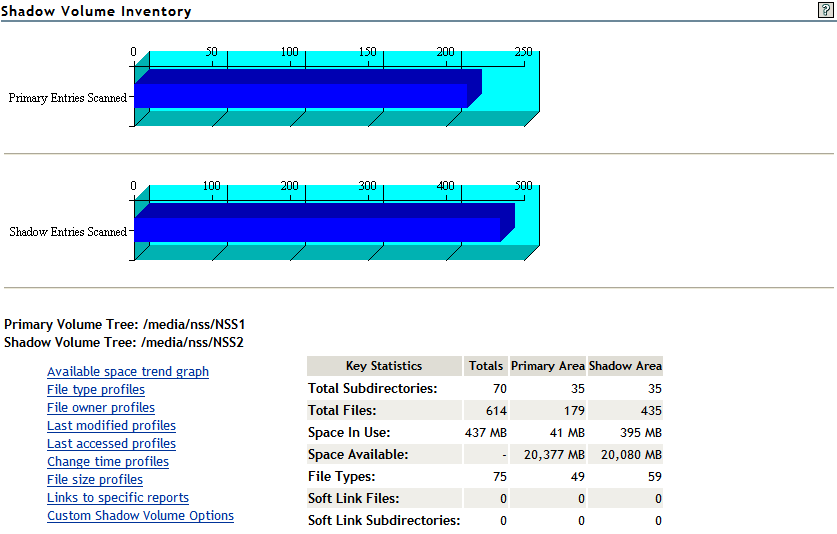
The inventory summary lists the number of files scanned on the primary storage area and the secondary storage area. It also lists key statistics for the primary storage area, the secondary storage area, and both areas combined as the shadow volume.
|
Key Statistics |
Description |
|---|---|
|
Total Subdirectories |
The total number of subdirectories in the volume. |
|
Total Files |
The total number of files in the volume. |
|
Space in Use |
The amount of space currently in use in the volume for data and metadata. On NSS volumes where salvage is enabled, the space in use includes space used by deleted files and directories. |
|
Space Available |
The amount of free space in the volume. |
|
File Types |
The number of different file types in use throughout the entire volume. |
|
Soft Link Files |
The NSS file system and NCP Server do not support soft links to files. This is a placeholder for future non-NCP support. |
|
Soft Link Subdirectories |
The NSS file system and NCP Server do not support soft links to subdirectories. This is a placeholder for future non-NCP support. |
The following figure is an example of the summary:
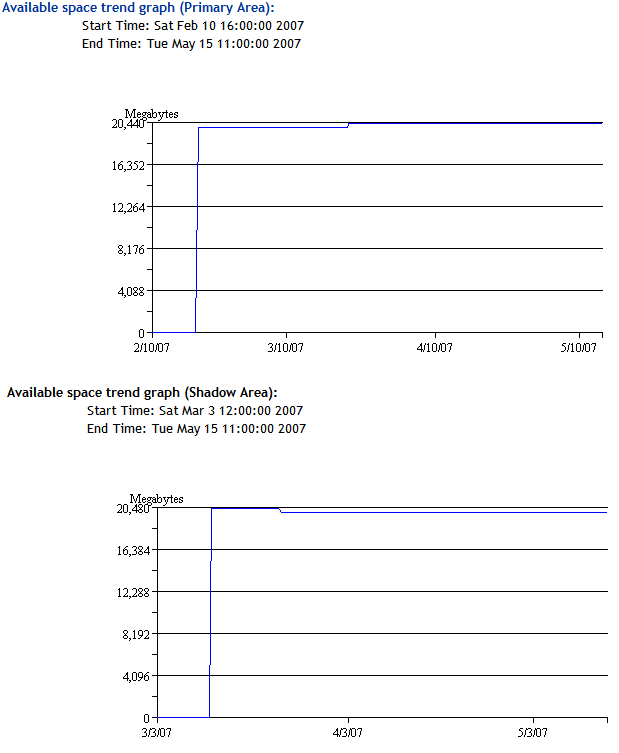
14.1.2 Available Space Trends
The Available Space Trends report shows the trends for space usage on the primary storage area and the secondary storage area. The following figure is an example of the Available Space Trend graphs:
14.1.3 Graphical Profiles
The Profiles portion of the inventory report graphically displays information about the shadow volume. Graphical profiles are displayed by size in bytes and file count for the following categories:
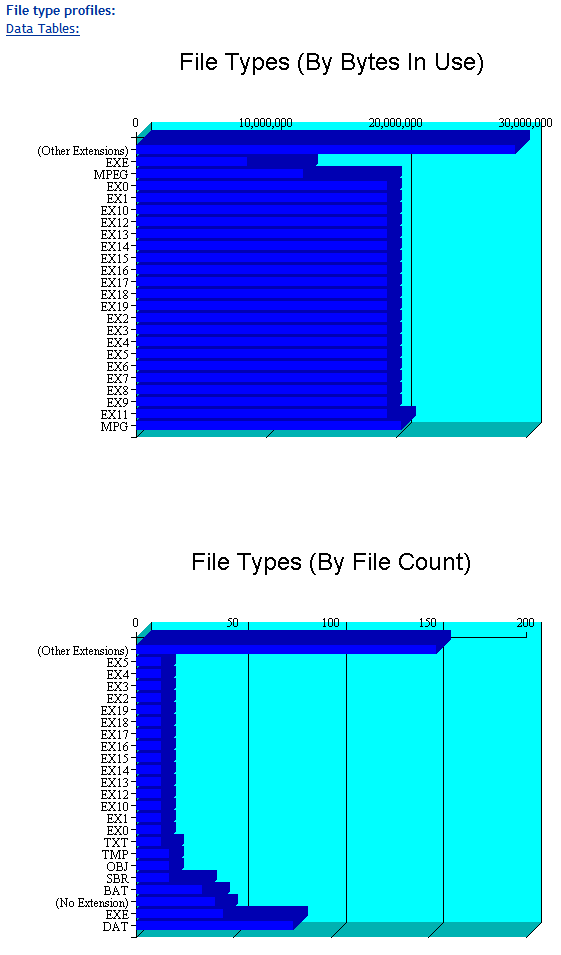
File Type Profiles
File Type Profiles indicates storage space usage by file types that are actually in use on your system, such as LOG, TDF, DAT, XML, EXE, and so on.
The following figure is an example of the File Type Profiles graphs:
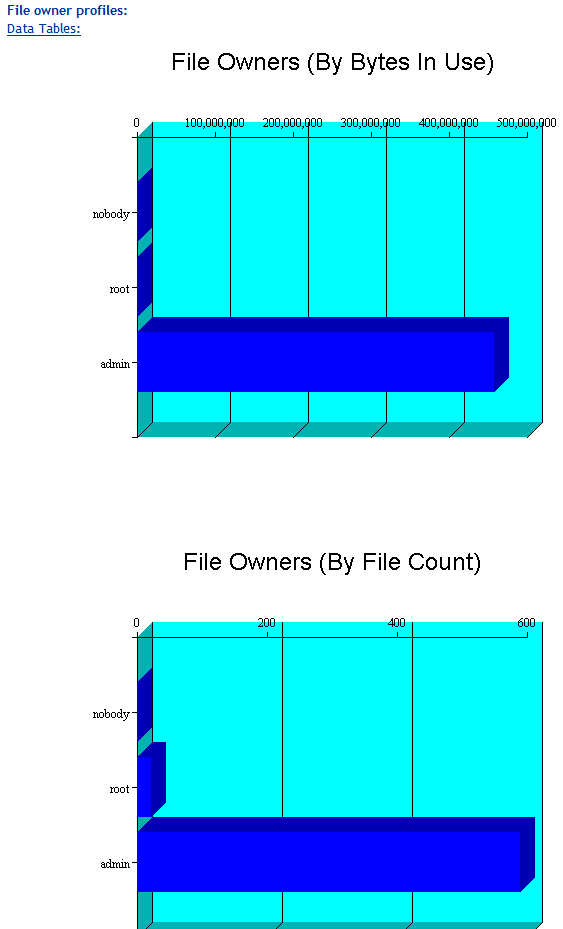
File Owner Profiles
File Owner Profiles indicates storage space usage by the designated owner of the file. It is not unusual in NCP to see the root user as the owner of files. For NCP volumes and NSS, file access is governed by the file system trustees assigned to the file, not the file owner. Trustees are users who have User objects defined in eDirectory, and who have been granted file system rights for the file. NCP tracks ownership via the user’s eDirectory GUID.
The following figure is an example of the File Owner Profiles graphs.
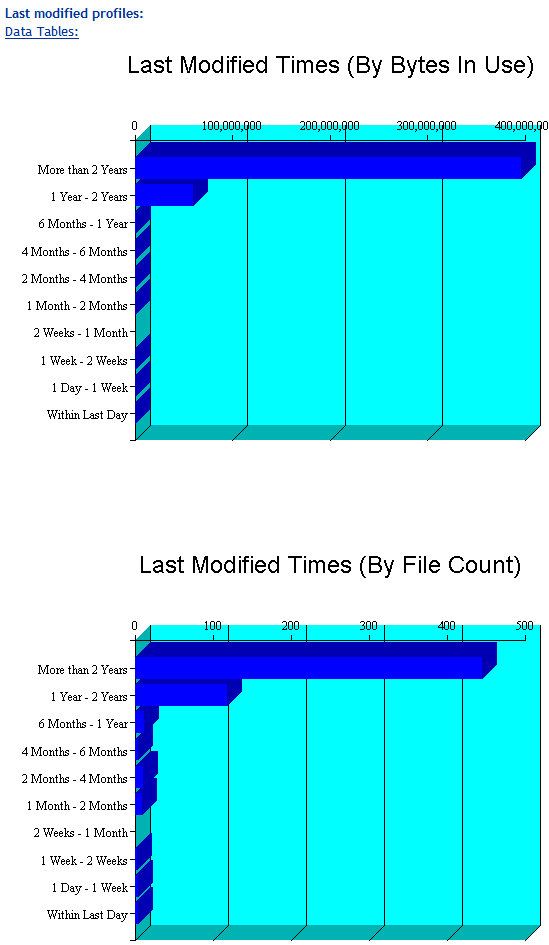
Time Stamp Profiles
Three time stamp profiles are generated:
-
Files Modified Profiles: Modified dates indicate the last time someone changed the contents of a file.
-
Files Accessed Profiles: Access dates indicate the last time someone accessed a file, but did not change the contents if this differs from the modified date.
-
Files Changed Profiles: Change dates indicate the last time someone changed the metadata of a file, but did not change the contents if this differs from the modified date.
Time stamps are grouped by the following time periods:
- More than 2 years
- 1 year to 2 years
- 6 months to 1 year
- 4 months to 6 months
- 2 months to 4 months
- 1 month to 2 months
- 2 weeks to 1 month
- 1 week to 2 weeks
- 1 day to 1 week
- Within last day
The following figure is an example of the File Modified Profiles graphs. Similar graphs are created for File Accessed Profiles and File Changed Profiles.
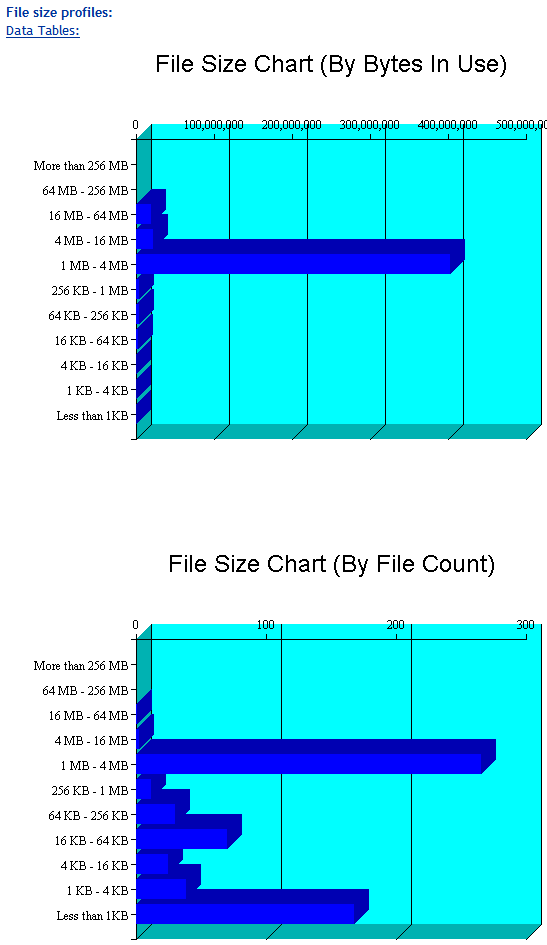
File Size Profiles
File Size Profiles reports the size of files, grouped by the following size ranges:
- More than 256 MB
- 64 MB to 256 MB
- 16 MB to 64 MB
- 4 MB to 16 MB
- 1 MB to 4 MB
- 256 KB to 1 MB
- 64 KB to 256 KB
- 16 KB to 64 KB
- 4 KB to 16 KB
- 1 KB to 4 KB
- Less than 1 KB
The following figure is an example of the File Size Profiles graphs:
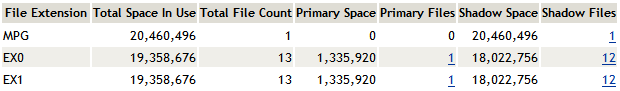
14.1.4 Tabular Profiles
Statistical data used to create the graphs is also available in tables that report statistics for the primary area, the secondary area, and both areas combined as the shadow volume. The count for file entries for the primary area and shadow (secondary) area are linked to detail reports that list the files matching that particular category and group. From the file lists, you have the option to copy, move, or delete one or multiple files.
For example, the following figure shows a few lines of a file-type information table:
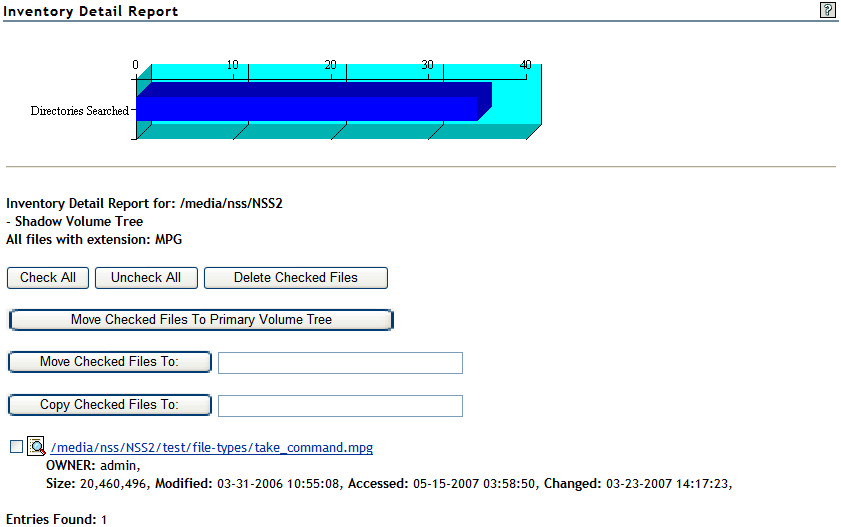
14.1.5 Inventory Detail Reports
An Inventory Detail Report lists all of the files that match a particular category and group for a file count entry in the tabular reports in the shadow volume inventory. You can select one or multiple files in the list, then select one of the following operations to be performed:
-
Move the selected volumes to the other file tree.
-
Move the selected files to a specified path on the server.
-
Copy the selected files to a specified path on the server.
-
Delete the selected files.
The action is performed on the selected files, and a confirmation list is displayed.

The following figure is an example of a detail report for file types that reside on the secondary volume:
14.1.6 Custom Shadow Volume Options
The Custom Shadow Volume Options section of the volume inventory allows you to generate reports based on key statistics of interest, and perform actions on them.
Volume Operations
You can perform one of the following volume operations on the files that match the search criteria you specify:
-
List primary area selected files
-
Move selected files from primary area to shadow area.
-
List shadow area selected files.
-
Move selected files from shadow area to primary area.
Search Patterns
In Search Patterns, you can specify wildcards and characters to select files by file names or extensions.
File Owner Restrictions
In File Owner Restrictions, select None or a user name. The search applies only to files where the file owner matches the specified owner.
Time Stamp Restrictions
You can specify one or multiple time stamps to consider for the search:
-
Last Modified Time
-
Last Accessed Time
-
Last Changed Time
If no time stamp is selected, time stamps are not considered in the search criteria.
If a time stamp is selected, you can specify one or multiple time ranges to consider for the search:
- Within last day
- 1 day to 1 week
- 1 week to 2 weeks
- 2 weeks to 1 month
- 1 month to 2 months
- 2 months to 4 months
- 4 months to 6 months
- 6 months to 1 year
- 1 year to 2 years
- More than 2 years
File Size Restrictions
You can specify one or multiple ranges of file sizes to consider for the search:
- Less than 1 KB
- 1 KB to 4 KB
- 4 KB to 16 KB
- 16 KB to 64 KB
- 64 KB to 256 KB
- 256 KB to 1 MB
- 1 MB to 4 MB
- 4 MB to 16 MB
- 16 MB to 64 MB
- 64 MB to 256 MB
- More than 256 MB