8.1 Security Administration
It is vital to secure each stage in the communication path between GroupWise and mobile devices.
8.1.1 Securing Communication with the LDAP Server
If you are using LDAP as your user source, you must secure the communication between your Mobility system and the LDAP server.
If your GroupWise system is configured to use LDAP authentication when users access their GroupWise mailboxes, your LDAP server is already set up for a secure SSL LDAP connection with your Mobility system. For more information, see the documentation for your version of GroupWise:
-
GroupWise 2014:
Trusted Root Certificates and LDAP Authentication
in the GroupWise 2014 Administration Guide -
GroupWise 2012:
Trusted Root Certificates and LDAP Authentication
in the GroupWise 2012 Administration Guide
You can enable and disable SSL for the LDAP connection in the LDAP section of the User Source page in the Mobility Admin console. For instructions, see Enabling and Disabling SSL for the Mobility Service LDAP Connection.
8.1.2 Securing Communication between the GroupWise Sync Agent and the GroupWise POA
The GroupWise Sync Agent communicates with the GroupWise POA as a SOAP client. In order to secure communication between the GroupWise Sync Agent and the GroupWise POA, the POA must be configured for secure SSL SOAP. For more information, see the documentation for your version of GroupWise:
-
GroupWise 2014: SOAP is enabled by default.
-
GroupWise 2012:
Supporting SOAP Clients
in the GroupWise 2012 Administration Guide
You can enable and disable SSL for the POA SOAP connections on the GroupWise Sync Agent Configuration page in the Mobility Admin console. For instructions, see Section 3.8, Enabling and Disabling SSL for POA SOAP Connections.
8.1.3 Securing Communication between the Device Sync Agent and Mobile Devices
In order to provide a secure SSL connection between the Device Sync Agent and mobile devices, you must provide a server certificate on the Mobility server.
For issues with specific types of certificates, see GroupWise Mobility Device Sync Agent SSL Issues.
For SSL issues with specific types of devices, see GroupWise Mobility Devices.
Using a Self-Signed Certificate on the Mobility Server
IMPORTANT:You should obtain a commercially signed certificate for use with your Mobility system as quickly as possible.
When you have the Mobility Service Installation program create a self-signed certificate for you, two certificate files are created in the /var/lib/datasync/device directory:
mobility.pem mobility.cer
When a mobile device connects to the Device Sync Agent, the Device Sync Agent passes the self-signed certificate file (mobility.pem) to the mobile device. In most cases, the mobile device accepts the self-signed certificate and connects successfully.
Some mobile devices do not automatically accept self-signed certificates in PEM format. If you choose to use a self-signed certificate and if users encounter connection problems with particular mobile devices, explain the procedure in Manually Downloading a Certificate to a Mobile Device to the users who are encountering connection problems. This procedure enables users to use the mobility.cer file instead of the mobility.pem file on their mobile devices.
The self-signed certificate generated by the Installation program is issued to “DataSync Web Admin” rather than to a specific hostname. Some mobile devices require that a self-signed certificate be associated with a specific hostname. For more information, see the documentation for your version of GroupWise:
-
GroupWise 2014:
Using a Self-Signed Certificate from the GroupWise Certificate Authority
in the GroupWise 2014 Administration Guide -
GroupWise 2012:
Generating a Self-Signed Certificate
in the GroupWise 2012 Administration Guide. Complete Step 1 through Step 4 inUsing YaST on Linux.
Do not complete Step 5. By default, YaST generates a single self-signed certificate file as required for use with your Mobility system.
Using a Commercially Signed Certificate on the Mobility Server
IMPORTANT:You should obtain a commercially signed certificate for use with your Mobility system as quickly as possible.
For more detailed instructions, see TID 7006904, How to Configure Certificates from a Trusted CA for the Device Sync Agent
in the Novell Support Knowledgebase.
Selecting a Certificate Authority (CA)
Choose a certificate authority (CA) from the many available on the Internet. If you do not want to immediately purchase a certificate, free temporary certificates are available from several websites, including:
Obtaining the Certificate
When you have selected a certificate authority, request a certificate in PEM format. If necessary, you can use a chained certificate or a wildcard certificate with your Mobility system. However, these more complex types of certificates are not recommended.
In order to obtain a certificate, you need to send the certificate authority a certificate signing request (CSR). For example, you can use OpenSSL to generate the CSR. For background information, see HOWTO Certificates.
-
In a terminal window on the Mobility server, become root by entering su - and the root password.
-
Change to a convenient directory where you want to create the CSR.
-
Create the key file:
-
Enter the following command:
openssl genrsa -des3 -out key_file_name.key 2048Replace key_file_name.key with a convenient name for the private key file, such as gw.key.
-
Enter and verify a pass phrase for the key file.
-
-
Create the CSR:
-
Enter the following command:
openssl req -new -key key_file_name.key -out csr_file_name.csr
Replace key_file_name.key with the key file that you created in Step 3.
-
Enter the pass phrase for the key file.
-
Enter the two-letter code for your country, such as US for the United States, DE for Germany, and so on.
-
Enter your state or province.
-
Enter your city.
-
Enter the name of your company or organization.
-
Enter your department or other organizational unit.
-
Enter your name.
-
Enter your email address.
-
(Optional) Enter a password for the CSR, or simply press Enter.
-
(Optional) Enter a secondary name for your company or organization, or simply press Enter.
-
NOTE:Depending on the method that you use to generate the CSR, you might be prompted for the type of web server where you plan to install the certificate. The Mobility Service uses the CherryPy web server.
The certificate authority returns one or more files to you. Save the files to a convenient location. These files might require modification for use in your Mobility system.
-
If the certificate authority included a password, remove the password. For instructions, see Removing a Password from a Key File.
-
If the certificate authority provided multiple files, combine them into a single file. For instructions, see Combining Files Received from a Certificate Authority.
Removing a Password from a Key File
If the key file provided by the certificate authority includes a password, you need to remove the password in order to use the key file in your Mobility system.
-
Check to see if the key file includes a password.
A password-protected key file includes the following line:
Proc-Type: 4,ENCRYPTED
-
Use the following command to remove the password:
openssl rsa -in original_file_name.key -out passwordless_file_name.key
Combining Files Received from a Certificate Authority
If you receive more than one file from the certificate authority, such as a certificate file and a key file, you must combine the contents into a single file with the following format:
-----BEGIN RSA PRIVATE KEY----- several_lines_of_private_key_text -----END RSA PRIVATE KEY----- -----BEGIN CERTIFICATE----- several_lines_of_server_certificate_text -----END CERTIFICATE-----
If the certificate authority provided an intermediate certificate, place it at the end of the file after the private key and the actual certificate.
Installing a Commercially Signed Certificate on the Mobility Server
-
(Conditional) If you have been using a self-signed certificate, rename the existing /var/lib/datasync/device/mobility.pem file.
-
Copy the certificate file received from the certificate authority to /var/lib/datasync/device.
-
Rename it to mobility.pem.
-
Restart the Mobility Service.
-
(Conditional) If a particular mobile device does not automatically accept the commercially signed certificate in PEM format, follow the instructions in Manually Converting a Certificate to DER Format for Use on Mobile Devices.
IMPORTANT:If you uninstall the Mobility Service, the certificate files associated with your Mobility system are also deleted. Back up commercially signed certificates in a location outside of /var/lib/datasync.
Manually Converting a Certificate to DER Format for Use on Mobile Devices
Some mobile devices do not automatically accept certificates in PEM format. If users encounter connection problems with particular mobile devices, you can convert the PEM file that you received from the certificate authority into DER format to resolve these connection problems.
-
Change to the /var/lib/datasync/device directory.
-
Execute the following command:
openssl x509 -in mobility.pem -inform PEM -out mobility.cer -outform DER
IMPORTANT:The output file name with the .cer extension must be in DER (Distinguished Encoding Rules) format.
-
Have users with connection problems follow the instructions in Manually Downloading a Certificate to a Mobile Device to use the mobility.cer file instead of the mobility.pem file.
Manually Downloading a Certificate to a Mobile Device
For background information, see Using a Self-Signed Certificate on the Mobility Server and Manually Converting a Certificate to DER Format for Use on Mobile Devices.
-
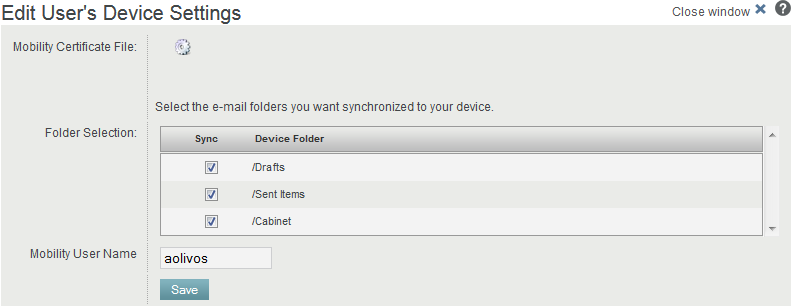
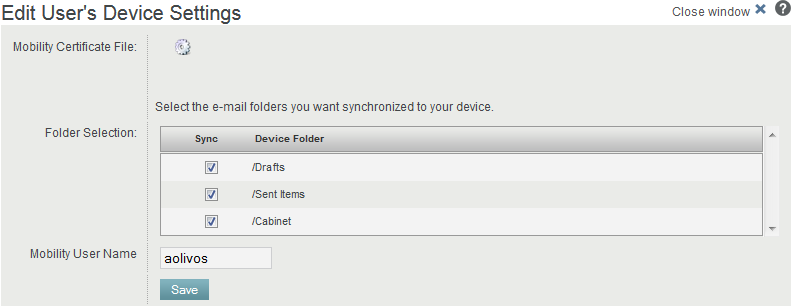
Access the Mobility Settings page of the Mobility Admin console on your mobile device at the following URL:
https://mobility_server:8120Replace mobility_server with the IP address or DNS hostname of the server where you installed the Mobility Service.
-
Log in using your network user name and password to display the Mobility Settings page on your mobile device.
-
Tap Device Settings.
-
In the Mobility Certificate File field, tap Download Certificate File
 .
.
NOTE:If you are the Mobility administrator and have associated your mobile device with the Mobility administrator account, you must navigate from the main Mobility Admin console page to the Mobility Certificate File field.
-
Save the mobility.cer file to a convenient location on your mobile device.
-
Import the certificate file into the certificate store on your mobile device.
For device-specific instructions, see the GroupWise Mobility Service Devices Wiki.
-
(Conditional) If you are not able to access the Mobility Settings page from your particular mobile device:
-
Access the Mobility Settings page in a web browser on your Windows or Linux desktop, then click Device Settings.
-
Click Download Certificate File
 .
.
-
Save the mobility.cer file on your Windows or Linux workstation.
-
Set up an IMAP email account on your mobile device, then email the mobility.cer file from your workstation to your mobile device.
or
Physically connect your mobile device to your workstation so that it appears as a drive on your workstation, then copy the mobility.cer file from your workstation to your device.
-
-
Import the certificate file into the certificate store on your mobile device.
Enabling and Disabling SSL for Device Connections
For instructions, see Section 4.9, Enabling and Disabling SSL for Device Connections.
Enabling a Password Security Policy for Device Connections
For instructions, see Section 4.3, Enabling a Device Password Security Policy.